In the modern corporate landscape, data is the new currency. Companies are increasingly leveraging sophisticated tools to monitor productivity, protect intellectual property, and ensure compliance. While monitoring external threats is a well-established practice, a new frontier has emerged: intensive internal surveillance. This practice, often colloquially termed “insnooping” (a portmanteau of “internal” and “snooping”), represents a significant shift in workplace dynamics, raising critical questions about ethics, legality, and the very nature of trust between employers and employees.
What Exactly is Insnooping?
Insnooping refers to the practice where an employer uses digital monitoring tools to observe, record, and analyze the activities of its employees during work hours. It goes beyond traditional, broad-stroke metrics like login times or network traffic volume. Insnooping involves a deeper, more granular level of surveillance that can feel personal and intrusive to the employee.
This can include:
-
Keystroke Logging: Recording every key pressed on an employee’s keyboard.
-
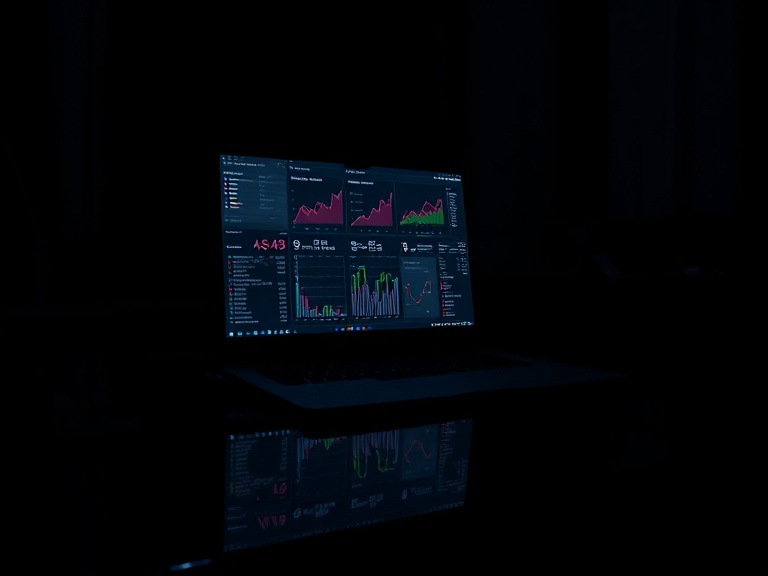
Screen Capture/Recording: Taking periodic screenshots or continuous video of an employee’s desktop.
-
Application and Website Tracking: Monitoring time spent on specific applications and logging every website visited, often in real-time.
-
Email and Message Scanning: Automatically scanning the contents of internal and external communications (e.g., Slack, Microsoft Teams, email) for keywords.
-
Webcam and Microphone Activation: Remotely activating a device’s camera or microphone, though this is highly controversial and often illegal without explicit consent.
-
Location Tracking: Using company-issued phones or badges to monitor an employee’s physical location within an office.
The core of insnooping is not just the collection of this data, but its use for continuous performance evaluation, behavior analysis, and sometimes, building a case for disciplinary action.
The Driving Forces Behind the Rise of Insnooping
The adoption of insnooping technologies is not without reason. Employers cite several justifications for its implementation:
-
Productivity and Performance Metrics: In an era of remote and hybrid work, managers often lack the visual cues of a traditional office. Insnooping tools provide data-driven “proof” of productivity, aiming to identify top performers and those who may be struggling or underworking.
-
Protection of Intellectual Property (IP): Companies invest millions in research and development. Insnooping acts as a digital sentry, designed to detect and prevent the unauthorized sharing or theft of sensitive data, trade secrets, and client information.
-
Cybersecurity Threat Mitigation: Employees can be the weakest link in cybersecurity, whether through falling for phishing scams or negligent data handling. Monitoring can help identify suspicious internal activity that could indicate a compromised account or a malicious insider threat.
-
Ensuring Legal and Regulatory Compliance: In highly regulated industries like finance or healthcare, companies are legally obligated to monitor communications to prevent fraud, insider trading, or violations of laws like HIPAA.
The High Cost of Constant Surveillance: Ethical and Cultural Implications
While the business arguments for insnooping may seem logical on the surface, the practice carries severe and often underestimated consequences for workplace culture and employee well-being.
-
Erosion of Trust: The fundamental pillar of any healthy employer-employee relationship is trust. The knowledge that one’s every digital move is being watched creates a culture of suspicion and paranoia. Employees feel like suspects rather than valued team members.
-
The Panopticon Effect: Named after a prison design where inmates feel they are always being watched, this effect leads to immense psychological stress. Employees may avoid taking necessary breaks or creative mental diversions for fear of being labeled “unproductive,” ironically leading to burnout and decreased long-term productivity.
-
Killing Innovation and Critical Thinking: Innovation often requires unstructured time, experimentation, and the freedom to fail. A surveillance-heavy environment discourages this, pushing employees to stick to rigid, measurable tasks rather than engaging in the creative, collaborative, and sometimes messy work that drives real progress.
-
Data Privacy and Security Risks: The immense amount of personal data collected through insnooping—from accidental personal web searches to private messages glimpsed in screenshots—creates a massive security risk. This data trove is a prime target for hackers and could be misused by unethical managers.
Navigating the Legal Labyrinth
The legality of insnooping is a complex patchwork that varies significantly by country, state, and even municipality. Key legal principles generally include:
-
Notice and Consent: In many jurisdictions, employers are legally required to inform employees that they are being monitored. This is often done through an employee handbook, a policy agreement, or a pop-up notification upon login. Covert surveillance is much more legally fraught.
-
Reasonableness: There is often a legal test of whether the monitoring is reasonable. Monitoring work-issued devices on the corporate network is generally seen as more reasonable than monitoring personal devices or implementing surveillance in private areas like break rooms.
-
Purpose Limitation: The collected data should only be used for the stated purpose (e.g., security) and not for unrelated discrimination or harassment.
Employees concerned about their company’s monitoring practices should carefully review their employment contract and company handbook and consult local labor laws.
Striking a Balance: Principles for Responsible Monitoring
It is possible for companies to protect their interests without resorting to dystopian levels of insnooping. The key is to adopt a transparent, principle-based approach:
-
Radical Transparency: Be unequivocally clear about what is being monitored, how, why, and who has access to the data. Employees should not have to guess.
-
Proportionality: The level of monitoring should be proportional to the risk. Not every employee needs keystroke logging. High-level access to IP may warrant more scrutiny than other roles.
-
Focus on Output, Not Activity: The healthiest cultures measure employees on their results and output—the quality of their work, projects completed, goals met—rather than micromanaging their daily activity patterns.
-
Respect for Privacy: Establish clear boundaries. Personal use of company devices during breaks should be expected and allowed without punishment, provided it doesn’t violate security policies.
By shifting the focus from punitive surveillance to enabling and trusting employees, companies can foster a more positive, innovative, and ultimately more productive environment.
Informational FAQs on Insnooping
Q1: Is insnooping legal?
A: The legality depends entirely on your location and the specific methods used. Generally, employers have a right to monitor activity on their own equipment and networks, but they are often required to notify employees that such monitoring is taking place. Covert surveillance (monitoring without notice) is illegal in many places.
Q2: How can I tell if my employer is insnooping on me?
A: Look for clues in your employment contract, company handbook, or IT policy. You may also be required to install monitoring software or see a notification upon logging into your computer that states monitoring is active. If you are unsure, you can ask your HR department directly about the company’s monitoring policies.
Q3: What can I do if I feel my employer’s monitoring is excessive or invasive?
A: First, review the company’s stated policy to understand what is permitted. If you believe the monitoring violates company policy or local labor laws, you can raise the issue with HR, a manager you trust, or a union representative. For serious violations, consulting with an employment lawyer is advisable.
Q4: Can my employer monitor me through my webcam without telling me?
A: In virtually all cases, remotely activating a webcam without explicit and continuous consent is highly illegal and a gross invasion of privacy. This would likely violate wiretapping and privacy laws.
Q5: Does using a VPN or incognito mode protect me from workplace monitoring?
A: No. Company-installed monitoring software operates at the device or operating system level, meaning it can track all your activity regardless of your browser mode or a VPN, which only masks your traffic from your internet service provider, not from your employer.
Q6: What’s the difference between legitimate monitoring and insnooping?
A: The line is often defined by transparency, proportionality, and purpose. Legitimate monitoring is disclosed, focused on security and high-level productivity metrics, and used to protect company assets. Insnooping tends to be secretive (or feels secretive), overly granular, and used for micromanagement and punitive measures.